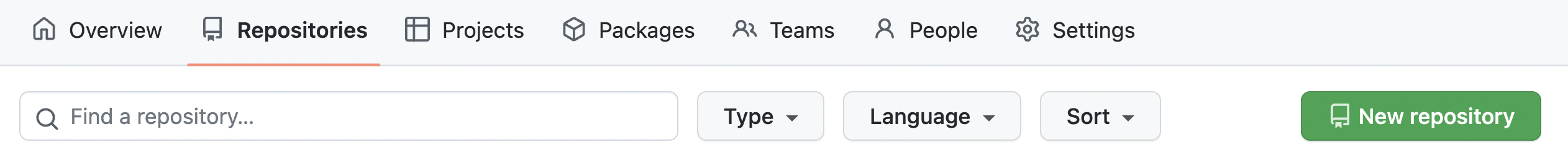
root can act as the owner of any object. Only root can perform certain sensitive administrative operation.Repositories, select New.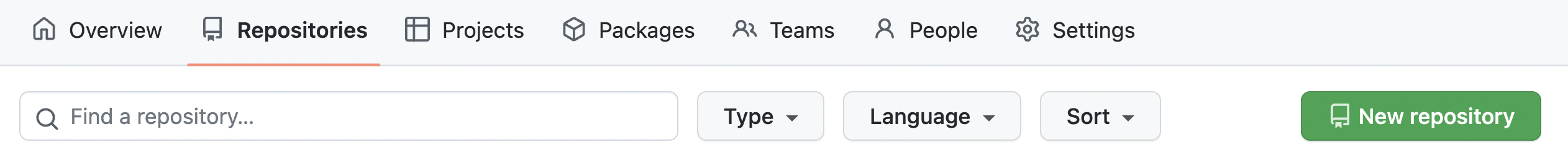
public.Add a README file box must be checked.Create repository when done.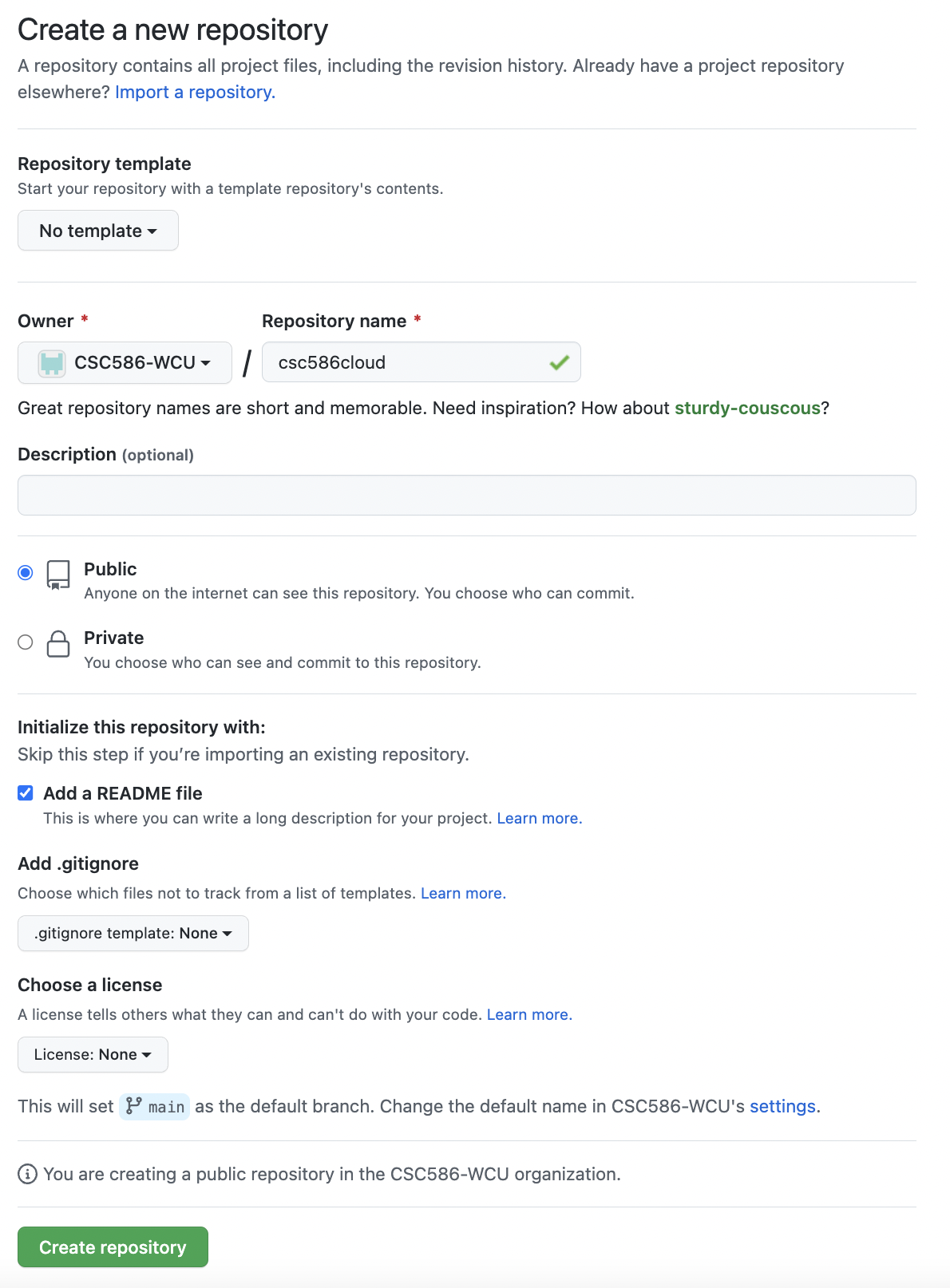
Add file and select Create new file.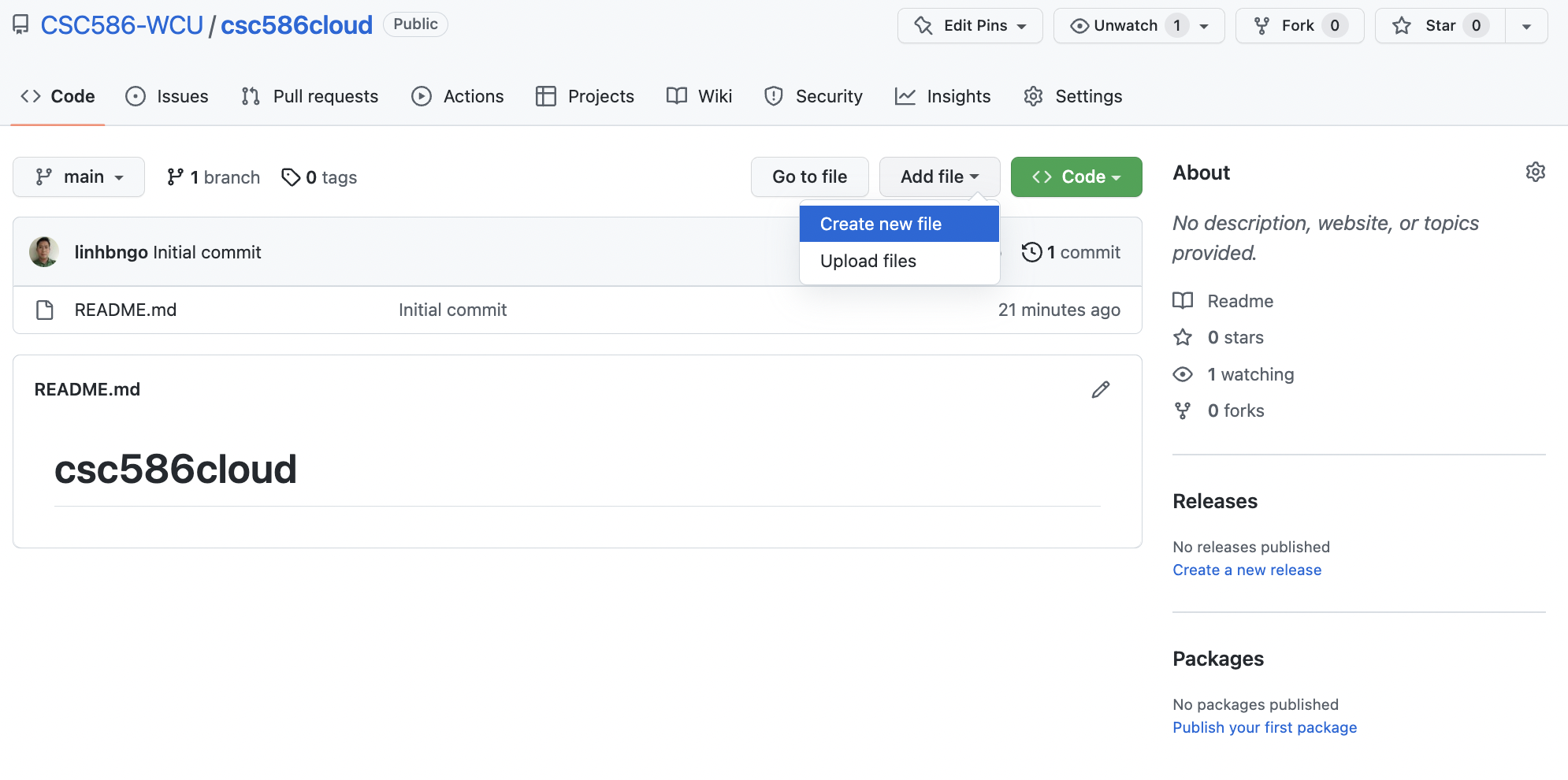
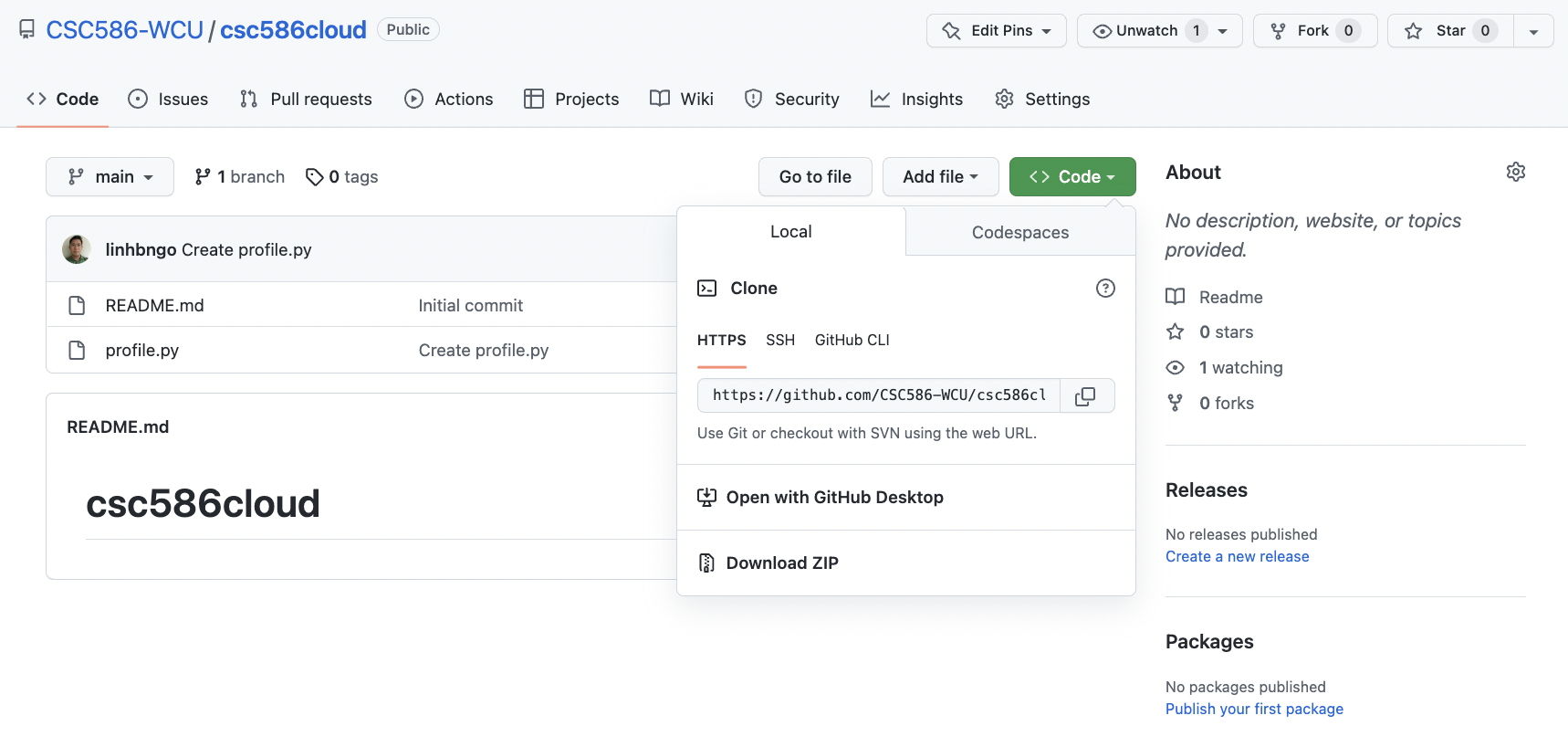
profile.py for the file name and enter the code below into the text editor.Commit new file when done.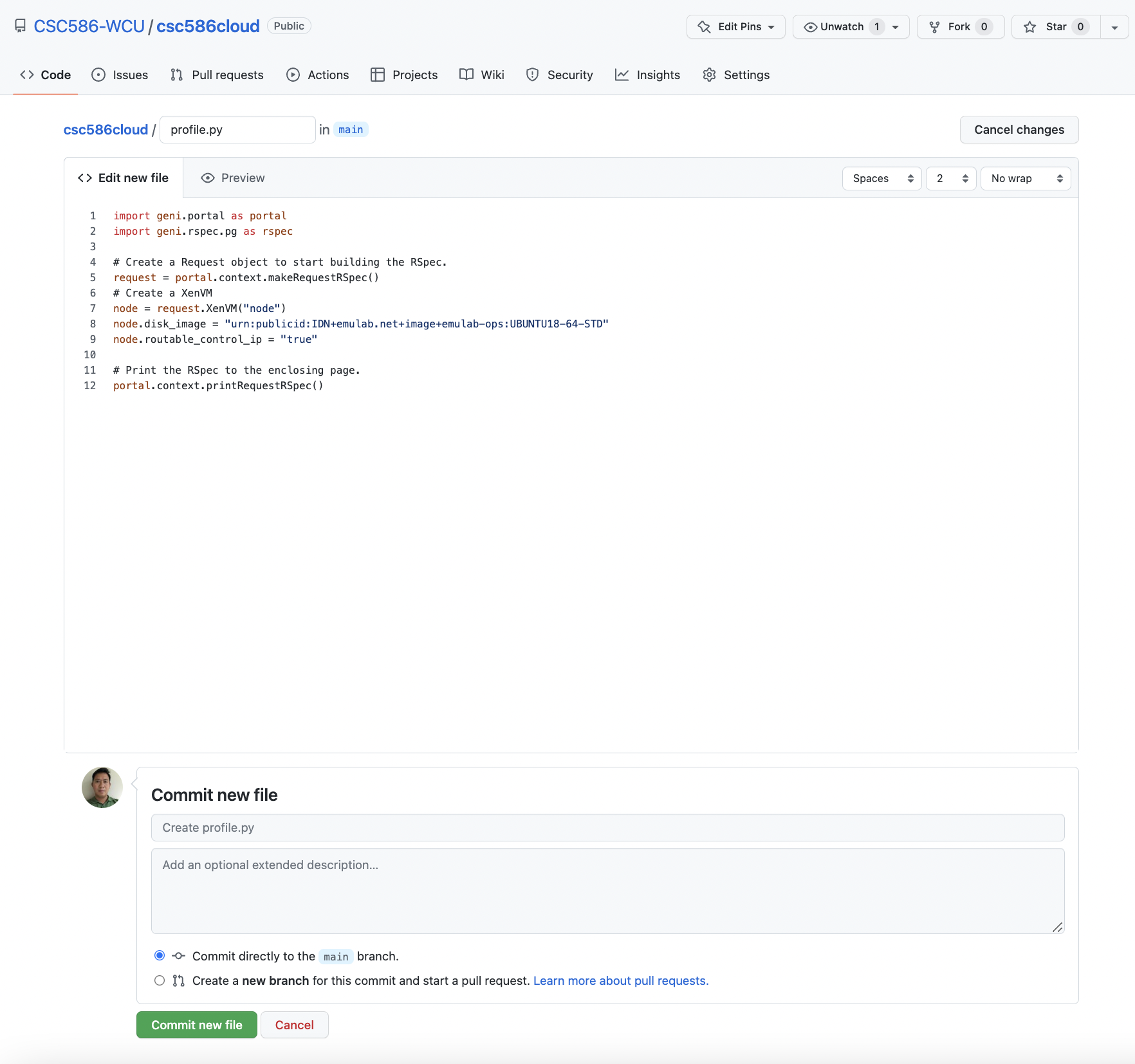
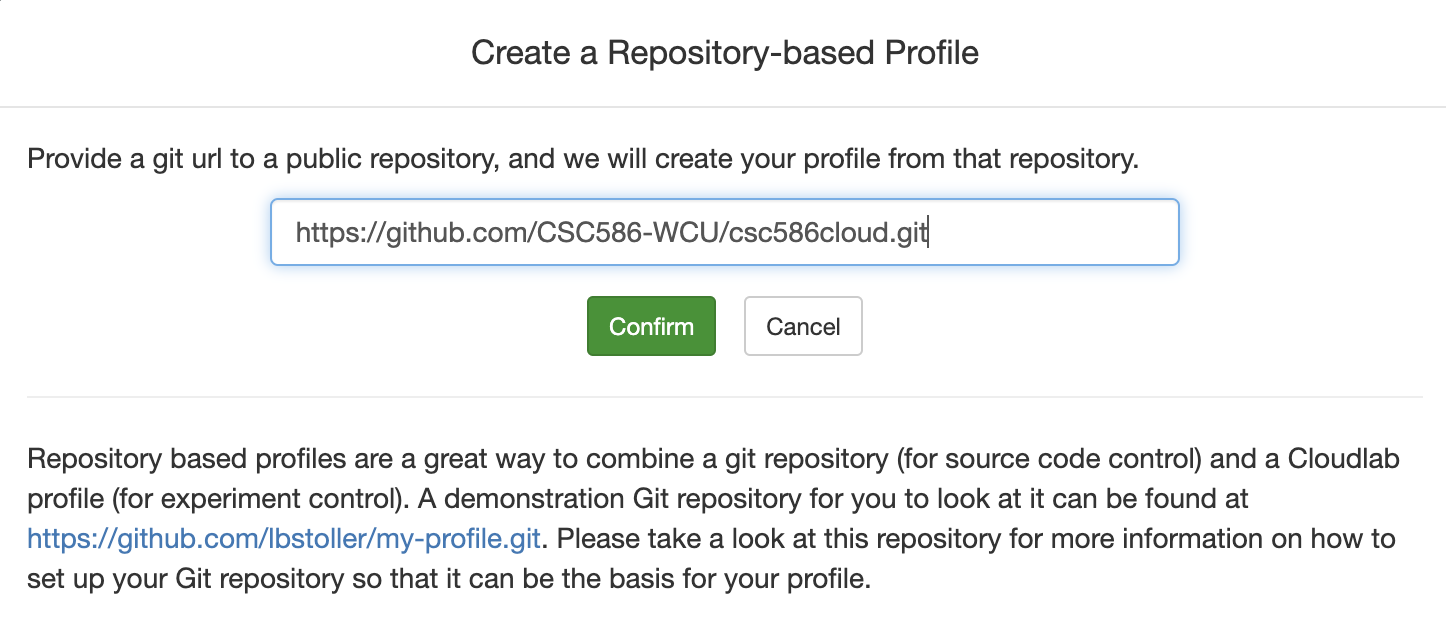
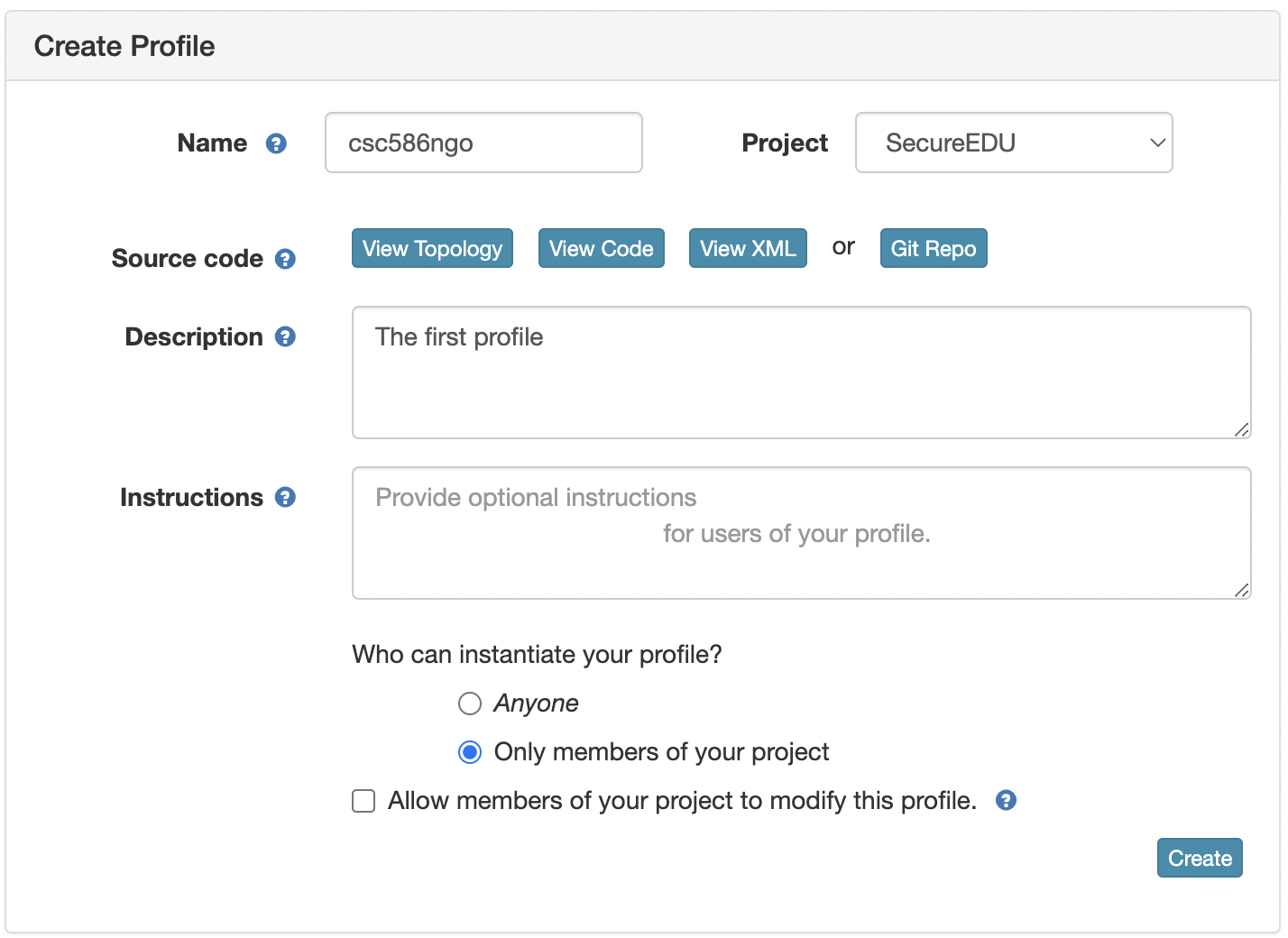
Experiments on top left, select Create Experiment Profile.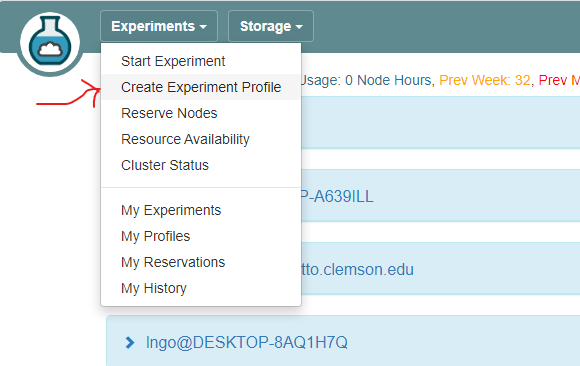
Git Repo 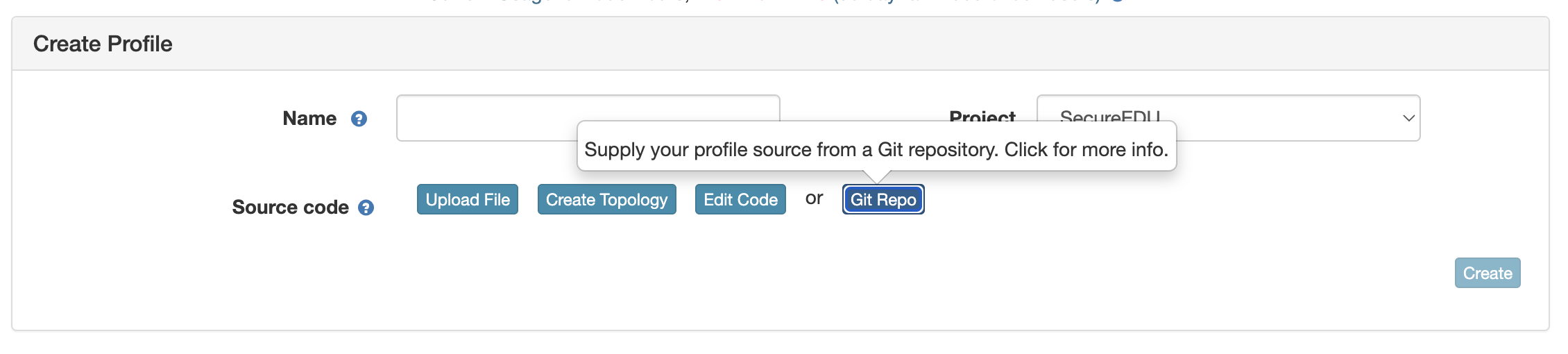
Instantiate to launch an experiment from your profile.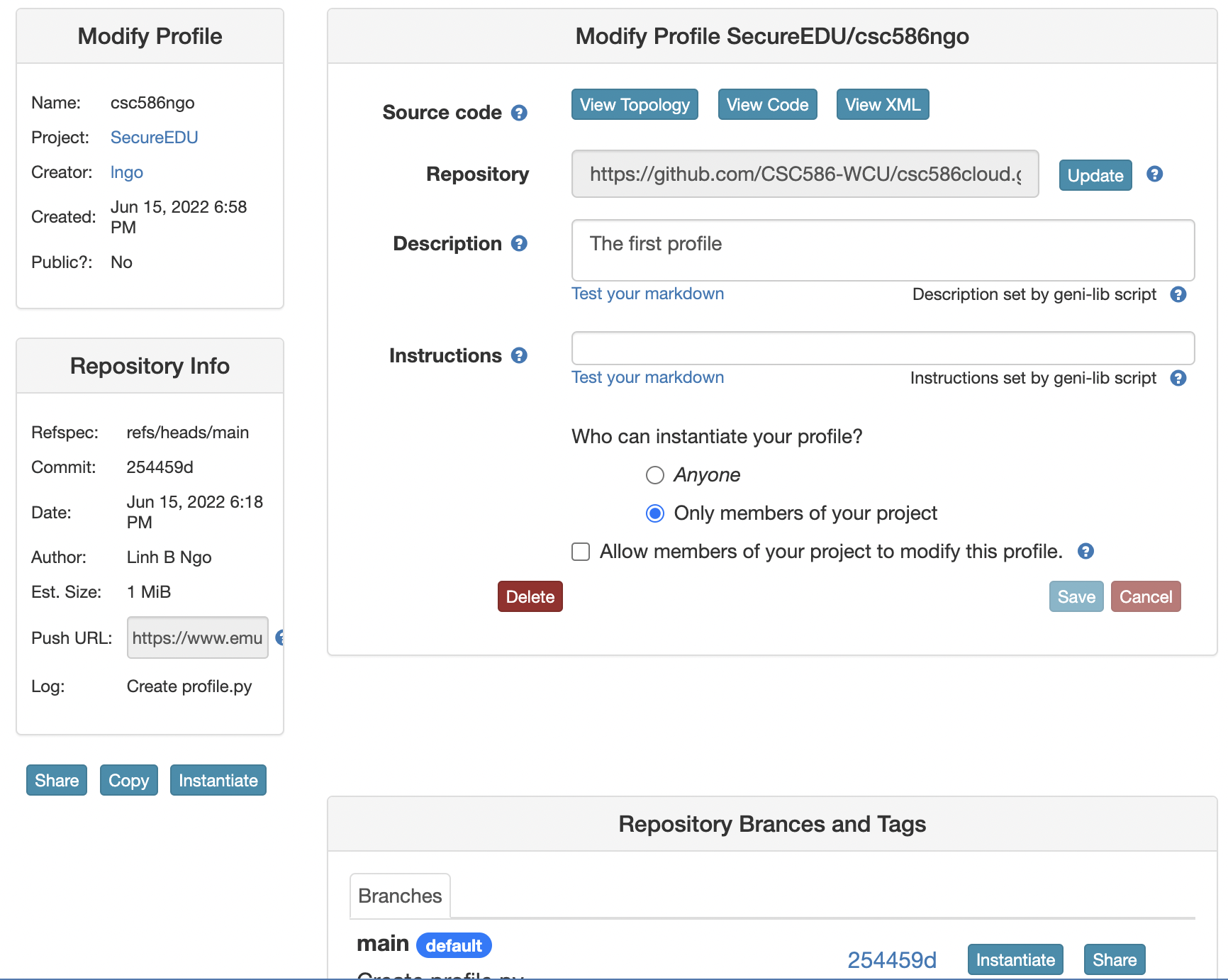
:alt: Instantiate an experiment from the profile
Next.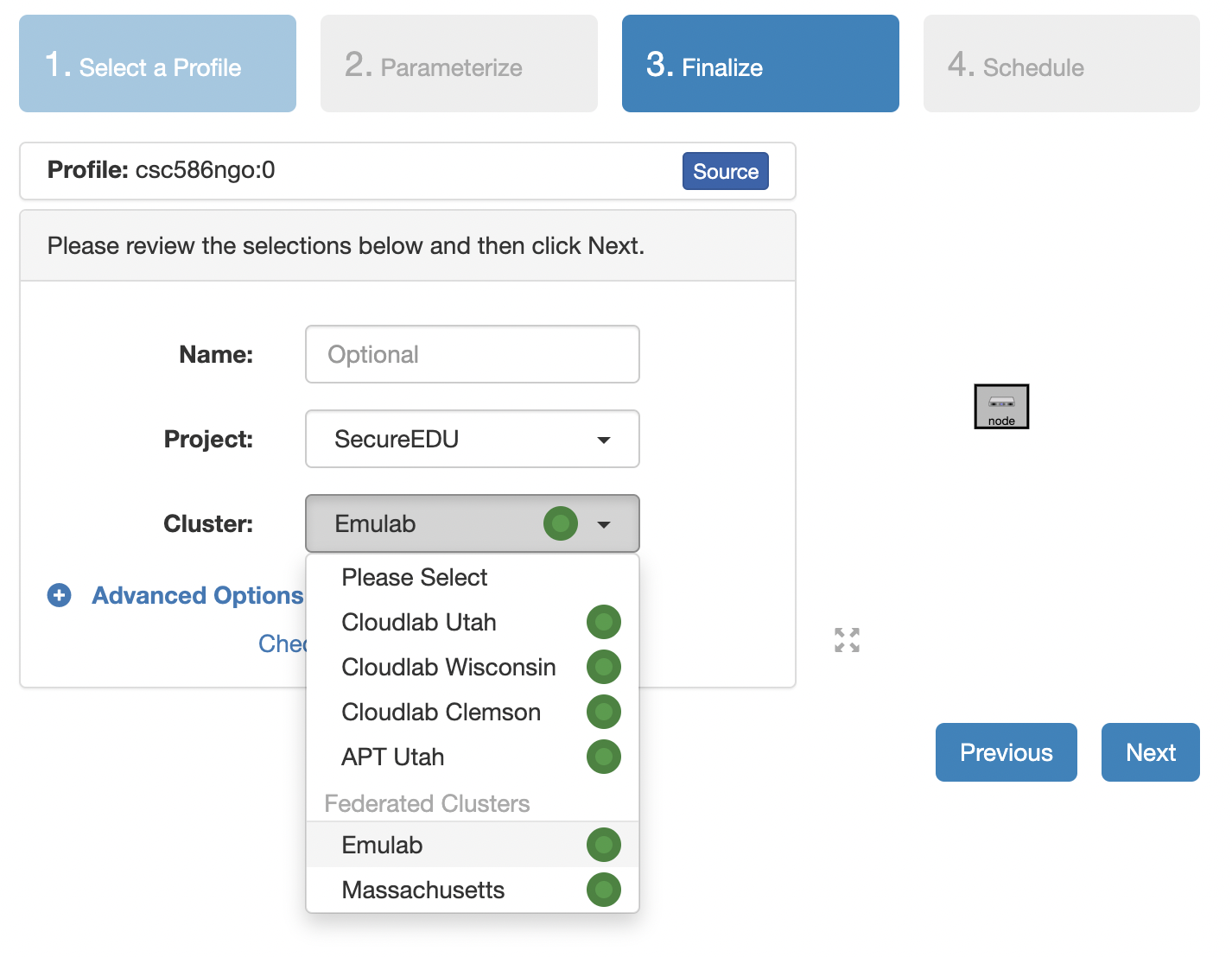
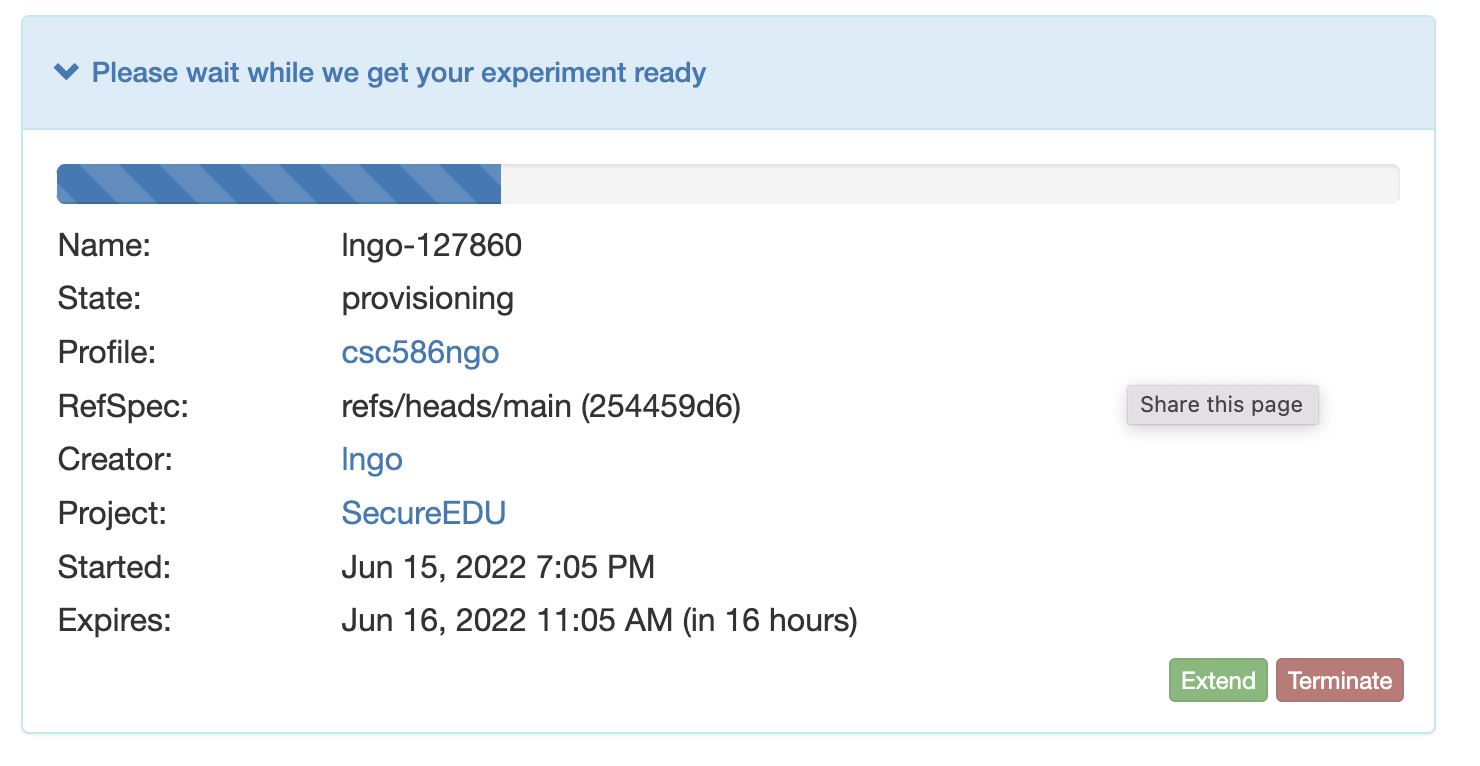
Finish.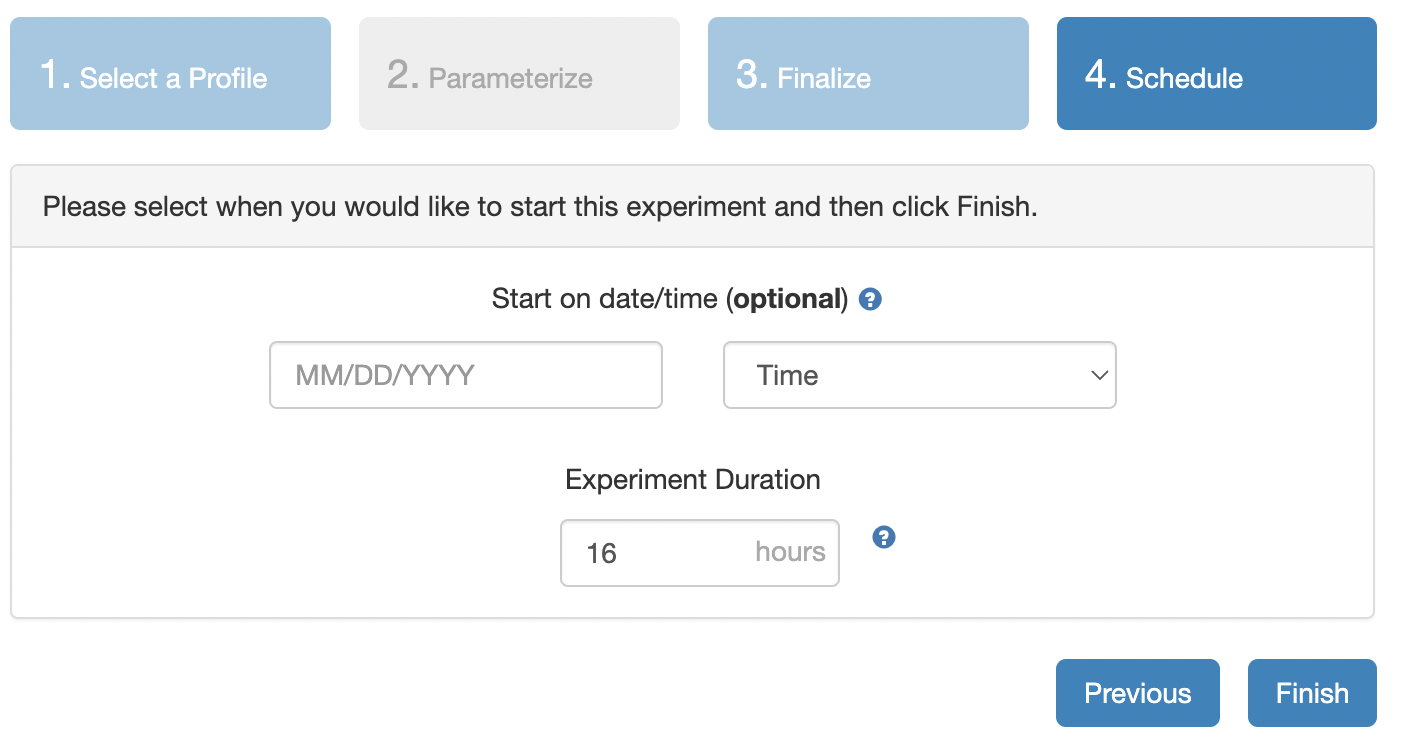
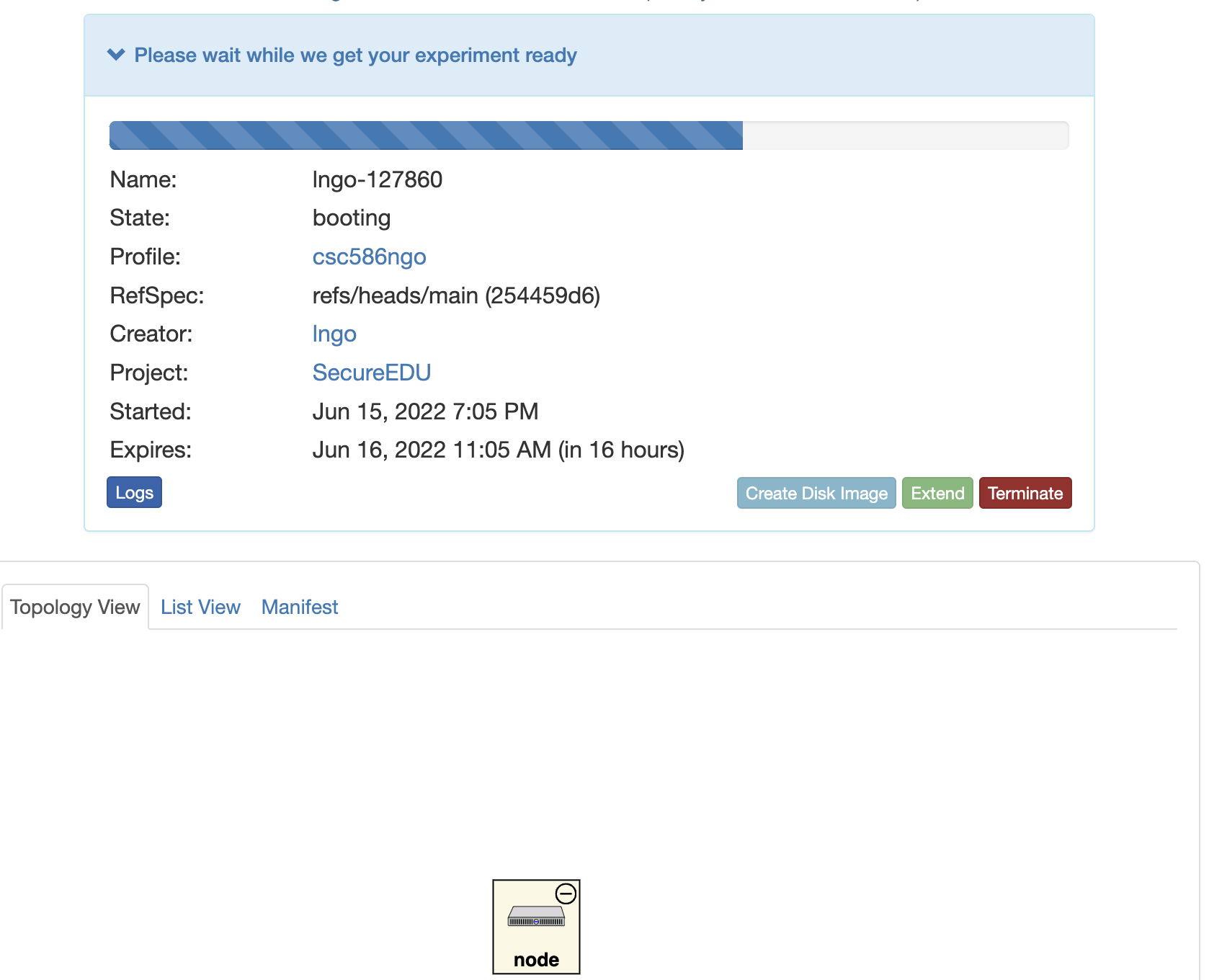
List View tab. Cluster and Status column.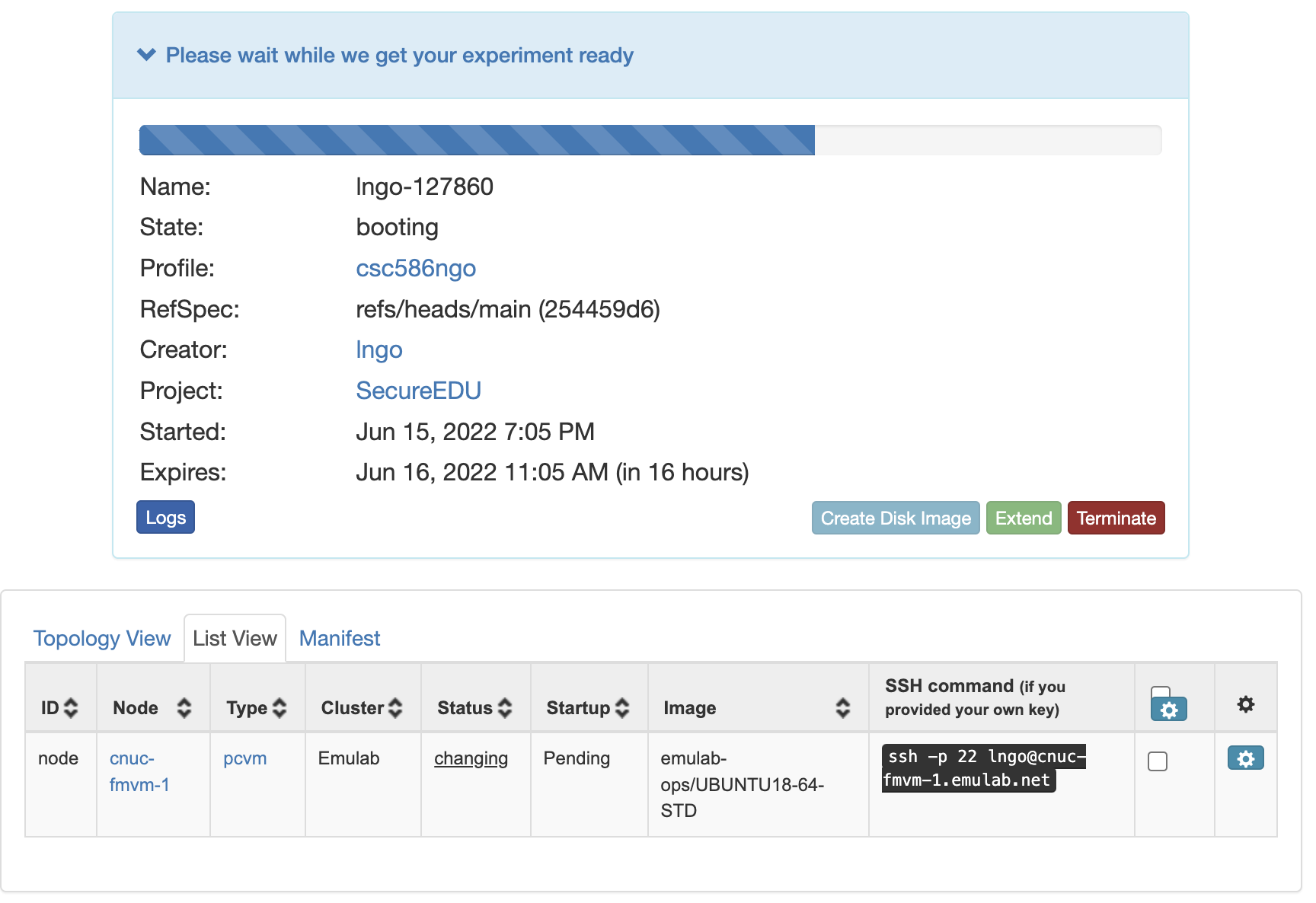
Cluster and Status column.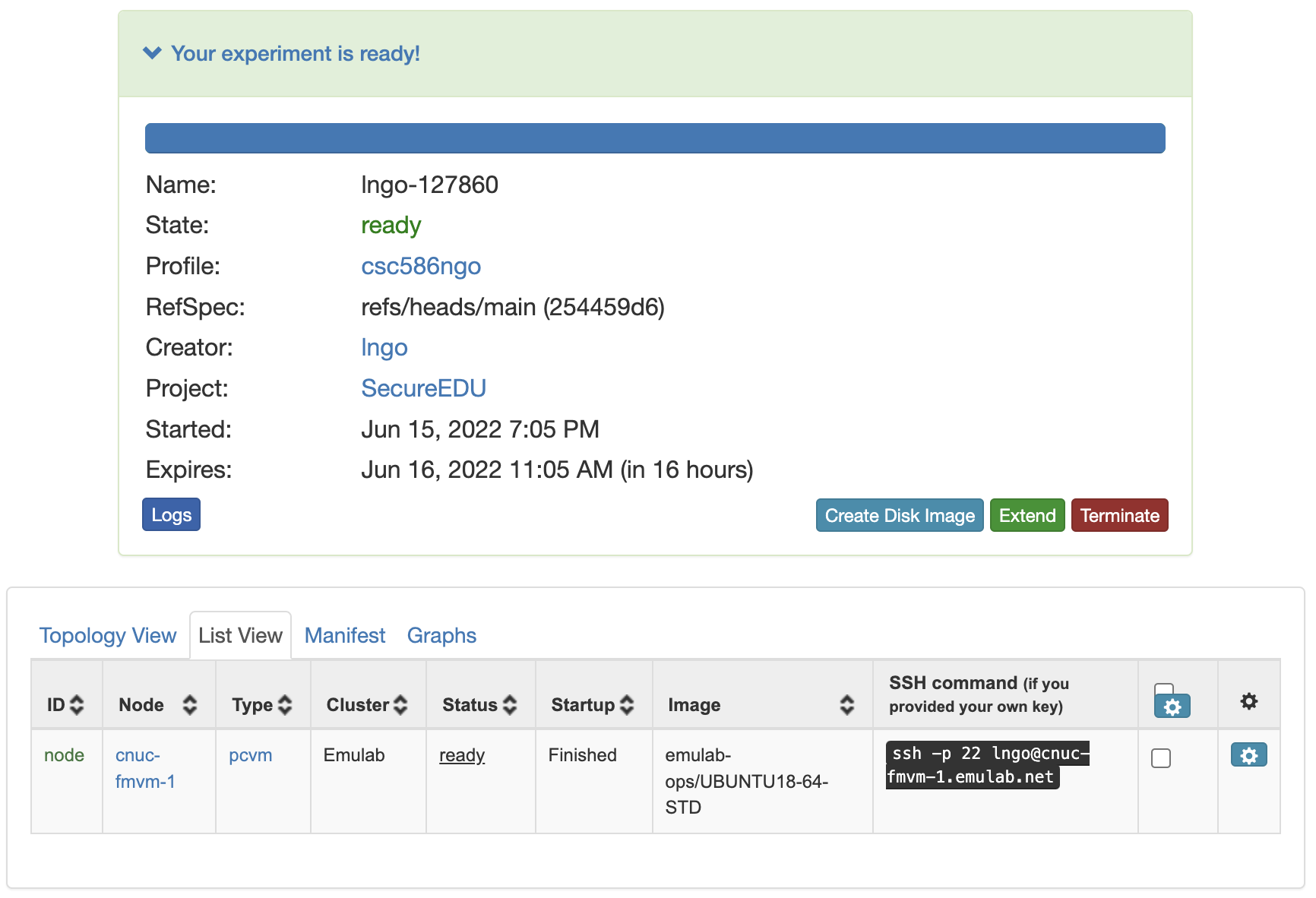
molly using the ssh command shown in the previous screenshot: yes and press Enter when inquired about The authenticity of host ... 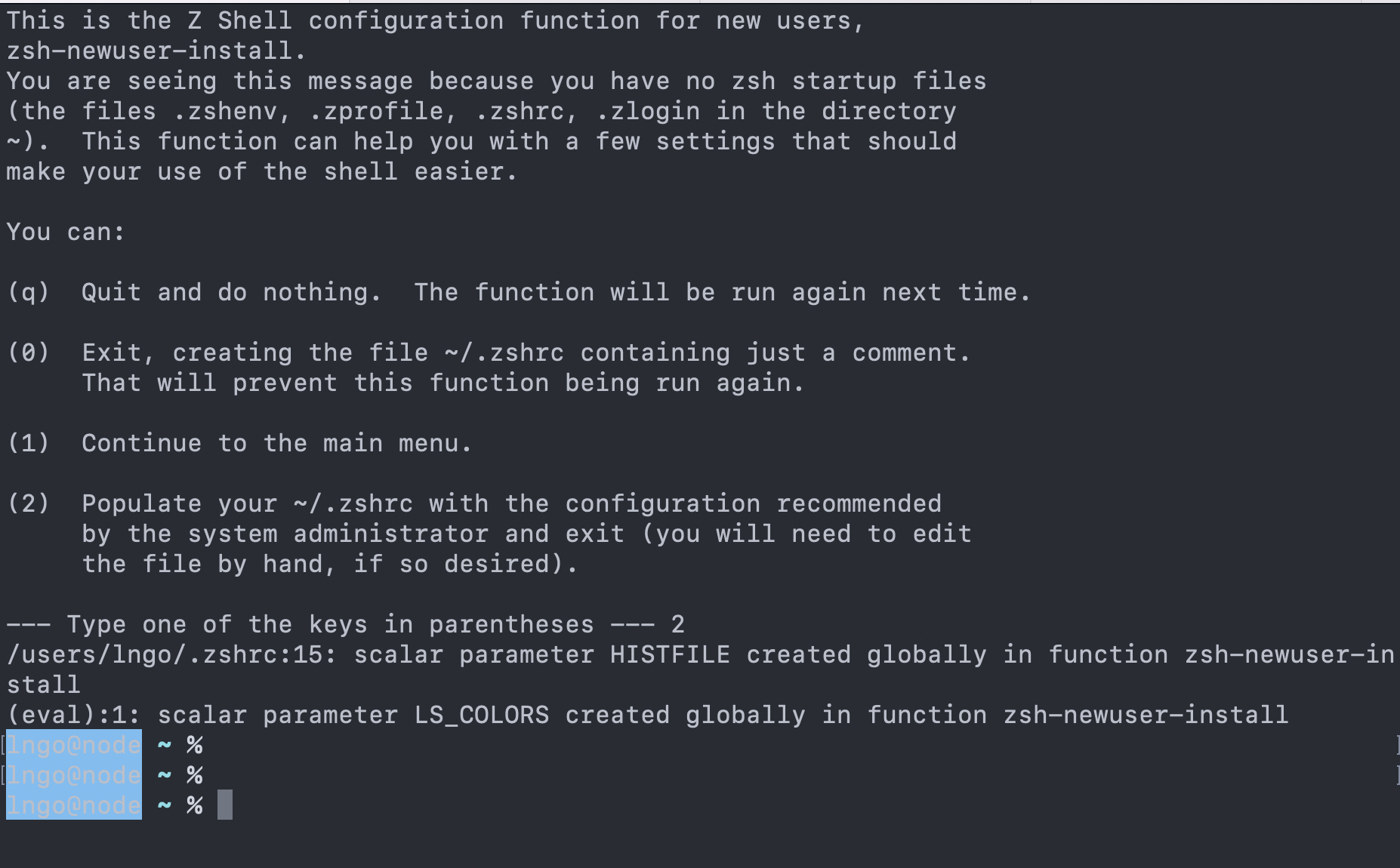
root can act as the owner of any object. Only root can perform certain sensitive administrative operation.sudo: Running the commands as another user. If there is no username provided, the user is going to be root. root account should always be very complicated and not be given out lightly.sudo power, meaning that they can execute commands in the name of other accounts, including root.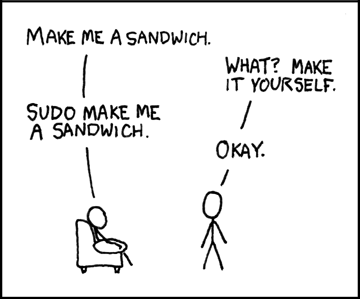
whoami: Give you the effective user id of the one running the shell.sudo:
1
2
3
4
whoami
sudo whoami
cat /etc/shadow
sudo cat /etc/shadow
setuid
1
id
non-root and non-sudo account.
1
2
3
4
5
6
7
8
9
man chown
man chmod
cat /etc/shadow
which cat
cp $(which cat) mycat
./mycat /etc/shadow
sudo chown root mycat
sudo chmod 4755 mycat
./mycat /etc/shadow
student.
1
sudo useradd -s /bin/sh -d /home/student -m student
student into an account with passwordless power.setuid alternative is difficult to manage due to potential capability leaks from complex software suites.AppArmor or Docker.namespaces) from which they see only a subset of the system’s files, network ports, and processes.discretionary access control (DAC) roles), and roles are assigned to users.roles can have hierarchical relationships (easier to administer)