units of plaintext with ciphertext, according to a fixed system.Units may be single letters, pairs of letters, triplets of letters, mixtures of the above, and so forth.
1
2
3
4
wget https://seedsecuritylabs.org/Labs_20.04/Files/Crypto_Encryption/Labsetup.zip
unzip Lapsetup
cd Lapsetup
docker-compose up -d
tr command
1
2
3
4
wget --no-check-certificate https://cs.wcupa.edu/lngo/data/enigma.txt
cat enigma.txt
tr [:upper:] [:lower:] < enigma.txt > lowercase.txt
cat lowercase.txt
1
2
3
4
tr 'a-z' 'vgapnbrtmosicuxejhqyzflkdw' < enigma.txt > cipher.txt
cat cipher.txt
tr 'vgapnbrtmosicuxejhqyzflkdw' 'a-z' < cipher.txt > plaintext.txt
cat plaintext.txt
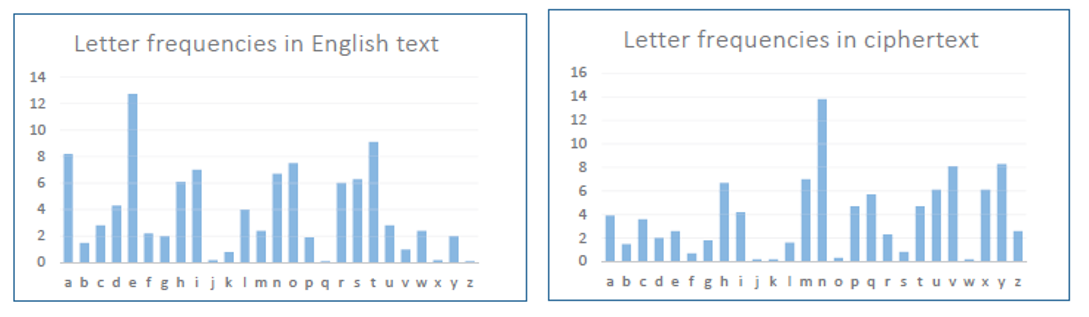
T, A, E, I, O TH, HE, IN, ER THE, AND, and ING 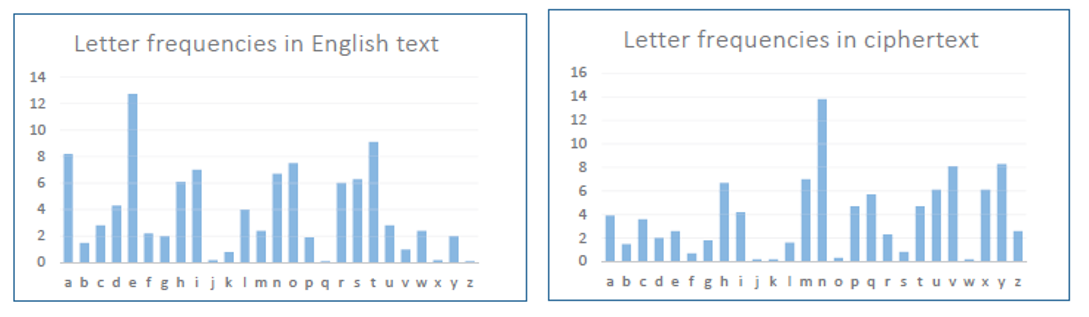
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
from collections import Counter
import re
TOP_K = 20
N_GRAM = 3
# generate all the n-grams for value n
def ngrams(n, text):
for i in range(len(text) - n + 1):
if not re.search(r'\s', text[i:i+n]):
yield text[i:i+n]
with open('cipher.txt') as f:
text = f.read()
for N in range(N_GRAM):
print("-----------------------------------")
print("{}-ngram (top {}):".format(N+1, TOP_K))
counts = Counter(ngrams(N+1, text))
sorted_counts = counts.most_common(TOP_K)
for ngram, count in sorted_counts:
print("{}: {}".format(ngram, count))
1
python3 freq.py
1
2
3
tr n E < cipher.txt
tr nt EH < cipher.txt
tr nty EHT < cipher.txt
1
2
wget --no-check-certificate https://www.cs.wcupa.edu/lngo/data/cipher_speech.txt
mv cipher_speech.txt cipher.txt
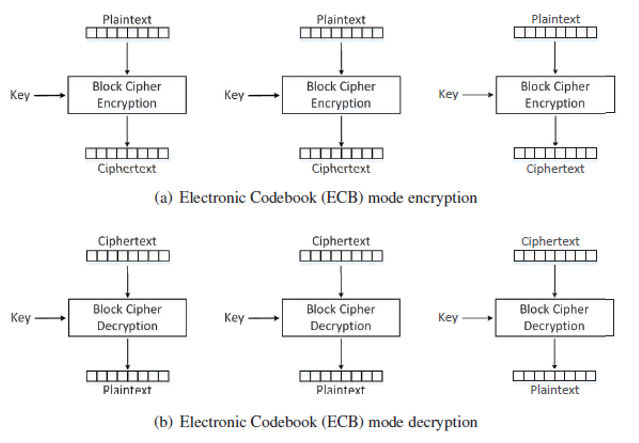
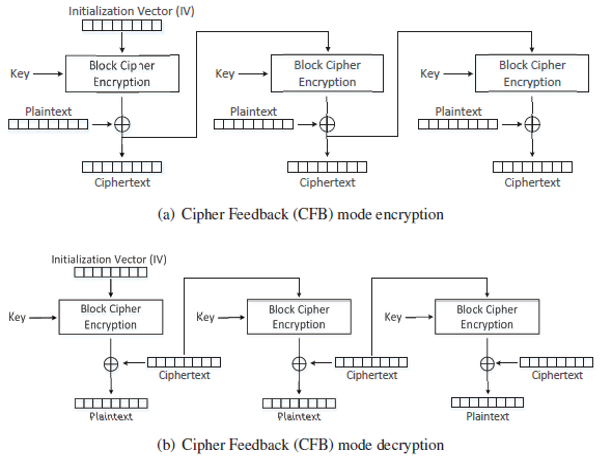
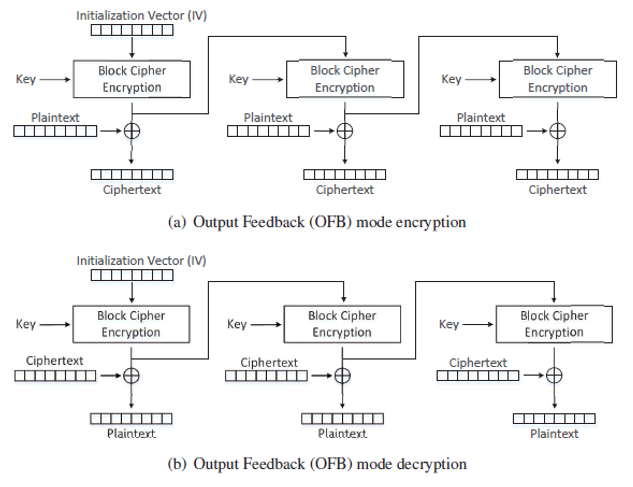
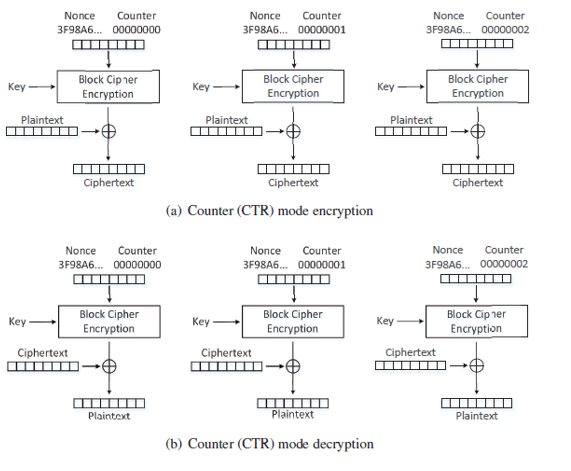
Encryption mode or mode of operation refers to the many ways to make the input of an encryption algorithm different.
Examples include:
1
2
3
4
5
echo "Hello Golden Rams!" > plain.txt
openssl enc -aes-128-ecb -e -in plain.txt -out cipher.txt -K 00112233445566778899AABBCCDDEEFF
cat cipher.txt
openssl enc -aes-128-ecb -d -in cipher.txt -out plain2.txt -K 00112233445566778899AABBCCDDEEFF
cat plain2.txt
IV is to ensure that even if two plaintexts are identical, their ciphertexts are still different, because different IVs will be used. 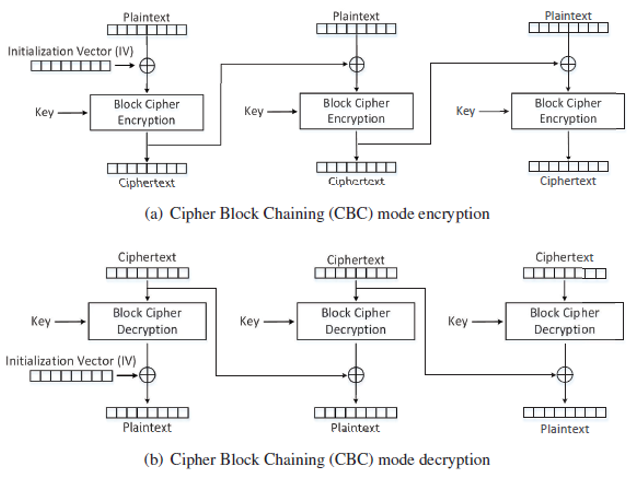
1
2
3
4
openssl enc -aes-128-cbc -e -in plain.txt -out cipher1.txt -K 00112233445566778899AABBCCDDEEFF -iv 000102030405060708090a0b0c0d0e0f
openssl enc -aes-128-ecb -e -in plain.txt -out cipher2.txt -K 00112233445566778899AABBCCDDEEFF -iv 000102030405060708090a0b0c0d0e0e
cat cipher1.txt
cat cipher2.txt
1
2
3
4
5
openssl enc -aes-128-cbc -e -in plain.txt -out cipher1.txt -K 00112233445566778899AABBCCDDEEFF -iv 000102030405060708090a0b0c0d0e0f
openssl enc -aes-128-cfb -e -in plain.txt -out cipher2.txt -K 00112233445566778899AABBCCDDEEFF -iv 000102030405060708090a0b0c0d0e0f
cat cipher1.txt
cat cipher2.txt
ls -l plain.txt cipher1.txt cipher2.txt
4ae71336e44bf9bf79d2752e234818a5
1
2
3
4
echo -n "John Smith......" > P1
openssl enc -aes-128-cbc -e -in P1 -out C1 -K 00112233445566778899AABBCCDDEEFF -iv 4ae71336e44bf9bf79d2752e234818a5
echo -n "4ae71336e44bf9bf79d2752e234818a5" | xxd -r -p > tmp_iv
md5sum tmp_iv
The next iv is 398d01fdf7934d1292c263d374778e1a
Since there is a limited number of candidates, let’s assume Even guesses that Bob voted for Mr. Ram, she creates P1_guessed and XOR it with the first and second iv values, and finally constructs the name for a write-in candidate.
1
echo -n "John Smith......" > P1_guessed
xor.py to do exclusive or
1
2
3
4
5
6
7
#!/usr/bin/env python3
from sys import argv
script, first, second = argv
aa = bytearray.fromhex(first)
bb = bytearray.fromhex(second)
xord = bytearray(x^y for x, y in zip(aa, bb))
print(xord.hex())
4a6f686e20536d6974682e2e2e2e2e2e.
1
xxd -p P1_guessed
1
2
chmod +x xor.py
./xor.py 4a6f686e20536d6974682e2e2e2e2e2e 4ae71336e44bf9bf79d2752e234818a5
1
./xor.py 00887b58c41894d60dba5b000d66368b 398d01fdf7934d1292c263d374778e1a
1
echo -n "39057aa5338bd9c49f7838d37911b891" | xxd -r -p > P2
1
2
3
openssl enc -aes-128-cbc -e -in P2 -out C2 -K 00112233445566778899AABBCCDDEEFF -iv 398d01fdf7934d1292c263d374778e1a
xxd -p C1
xxd -p C2