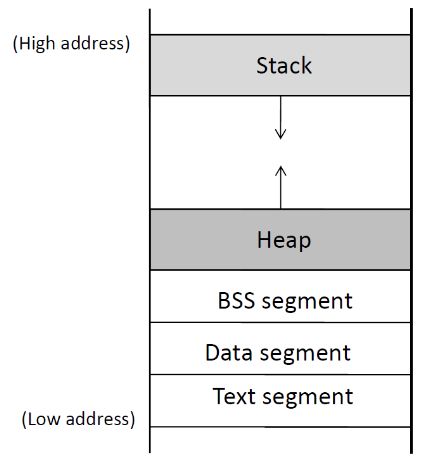
A running program is called a process.
Stack: is simple data structure with a LIFO (last-in-first-out access policy). Stack stores local variables defined inside functions, and data related to function calls (return address, arguments, etc)
mem_layout.c
1
2
3
4
5
sudo apt-get update
sudo apt-get install -y gcc-multilib g++-multilib
gcc -m32 -W -c mem_layout.c
gcc -m32 -o mem_layout mem_layout.o
size mem_layout mem_layout.o
Why don’t we see the stack and heap information?
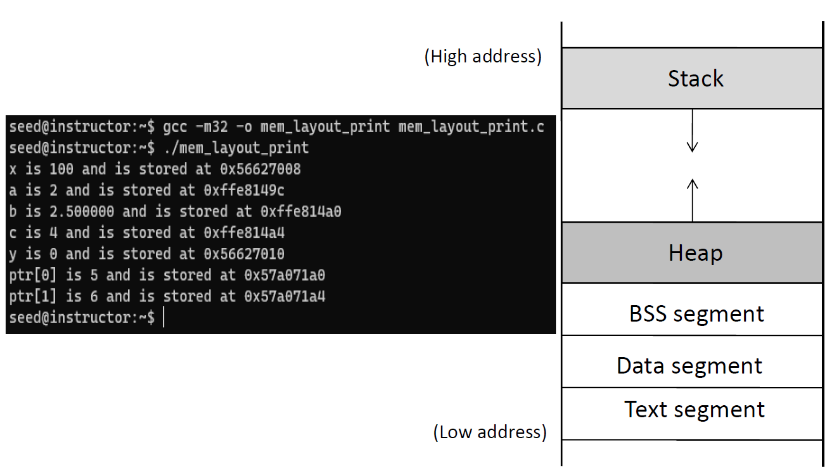
Create a file called mem_layout_print.c
mem_layout.c and edit.
1
2
gcc -m32 -o mem_layout_print mem_layout_print.o
./mem_layout_print
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
## Stack Memory
- When a function is called, a block of memory called stack frame will
be pushed onto the top of stack.
- A stack frame contains four regions:
- Arguments that are passed to the function (if they don't fit on the
general purpose registers)
- Return address (the address of the instructions right after
the function call
- Previous frame pointer
- Local variables of the function
- When the program first starts, the stack contains only one frame,
that of the main function.
<figure
>
<picture>
<!-- Auto scaling with imagemagick -->
<!--
See https://www.debugbear.com/blog/responsive-images#w-descriptors-and-the-sizes-attribute and
https://developer.mozilla.org/en-US/docs/Learn/HTML/Multimedia_and_embedding/Responsive_images for info on defining 'sizes' for responsive images
-->
<source
class="responsive-img-srcset"
srcset="/assets/img/courses/csc302/buffer-overflow/stack_mem_layout-480.webp 480w,/assets/img/courses/csc302/buffer-overflow/stack_mem_layout-800.webp 800w,/assets/img/courses/csc302/buffer-overflow/stack_mem_layout-1400.webp 1400w,"
type="image/webp"
sizes="95vw"
>
<img
src="/assets/img/courses/csc302/buffer-overflow/stack_mem_layout.png"
width="50%"
height="auto"
alt="Stack memory layout"
data-zoomable
loading="lazy"
onerror="this.onerror=null; $('.responsive-img-srcset').remove();"
>
</picture>
</figure>
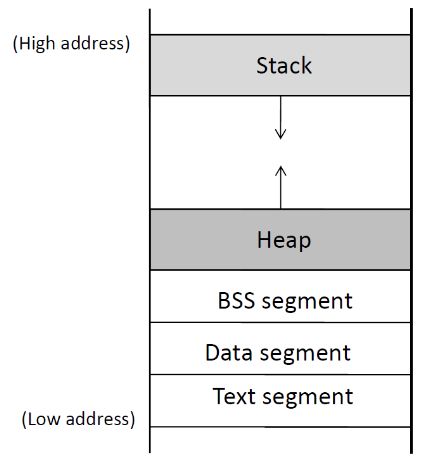
- We can call a function from inside a function.
- Any time we enter a function, a stack from is allocated on top of the stack.
- When the function returns, the allocated space is released.
<figure
>
<picture>
<!-- Auto scaling with imagemagick -->
<!--
See https://www.debugbear.com/blog/responsive-images#w-descriptors-and-the-sizes-attribute and
https://developer.mozilla.org/en-US/docs/Learn/HTML/Multimedia_and_embedding/Responsive_images for info on defining 'sizes' for responsive images
-->
<source
class="responsive-img-srcset"
srcset="/assets/img/courses/csc302/buffer-overflow/call_chain-480.webp 480w,/assets/img/courses/csc302/buffer-overflow/call_chain-800.webp 800w,/assets/img/courses/csc302/buffer-overflow/call_chain-1400.webp 1400w,"
type="image/webp"
sizes="95vw"
>
<img
src="/assets/img/courses/csc302/buffer-overflow/call_chain.png"
width="50%"
height="auto"
alt="Chain of function calls"
data-zoomable
loading="lazy"
onerror="this.onerror=null; $('.responsive-img-srcset').remove();"
>
</picture>
</figure>
One of the oldest and most well-known attacks.
strcpy_overflow.c
1
2
gcc -m32 -o strcpy_overflow strcpy_overflow.c
./strcpy_overflow
1
2
3
4
git clone https://github.com/longld/peda.git
echo "source $HOME/peda/peda.py" > $HOME/.gdbinit
gcc -m32 -g -o gdb_strcpy_overflow strcpy_overflow.c
gdb gdb_strcpy_overflow
b main) and start running (run).si: executing the next instruction (machine or code instruction). ni if we don’t want to step into that instruction.stack.c 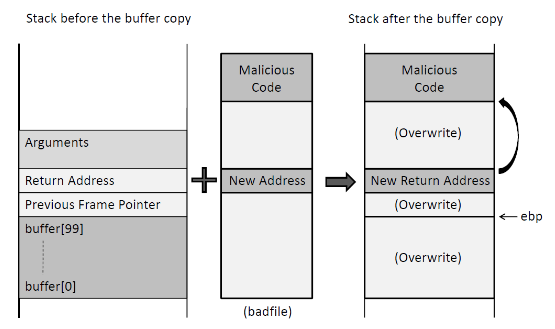
mem_layout_print several times
1
2
3
./mem_layout_print
./mem_layout_print
./mem_layout_print
1
echo 0 | sudo tee /proc/sys/kernel/randomize_va_space
1
2
3
./mem_layout_print
./mem_layout_print
./mem_layout_print
-z execstack-fno-stack-protector
1
2
3
4
5
6
7
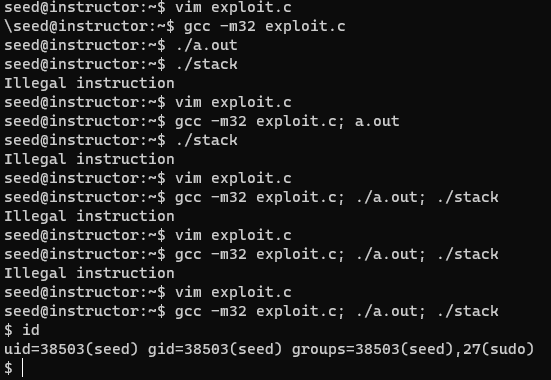
gcc -m32 -o stack -z execstack -fno-stack-protector stack.c
sudo chown root stack
sudo chmod 4755 stack
echo "aaaa" > badfile
./stack
echo "aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa" > badfile
./stack
Why segmentation fault?
foo() will be for us to find out where the malicious code is located (and hence set the relevant jump address)?
1
2
3
4
gcc -m32 -g -o gdb_stack -z execstack -fno-stack-protector stack.c
rm badfile
touch badfile
gdb gdb_stack
1
2
3
4
5
6
break foo
run
print $ebp
print &buffer
print <hex address of ebp> - <hex address of buffer>
quit
108 (decimal) or 0x6C (hex)?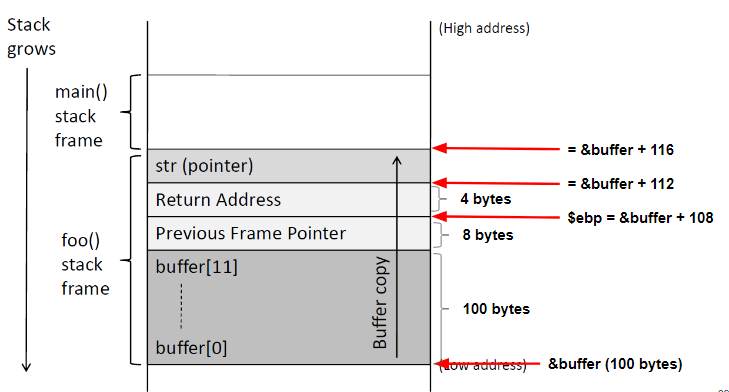
/bin/sh command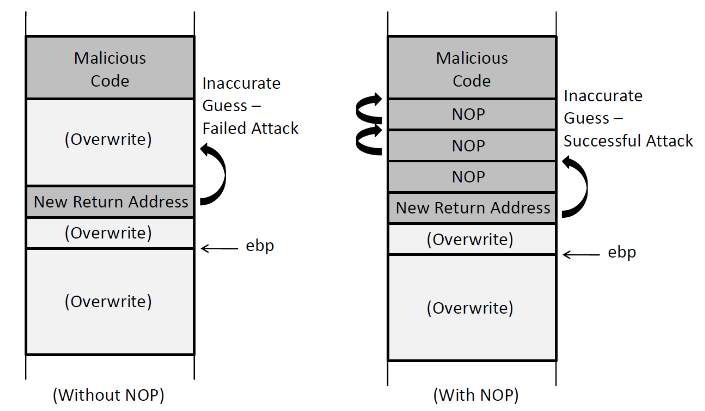
-fno-stack-protector kernel.randomize_va_space ```