1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
|
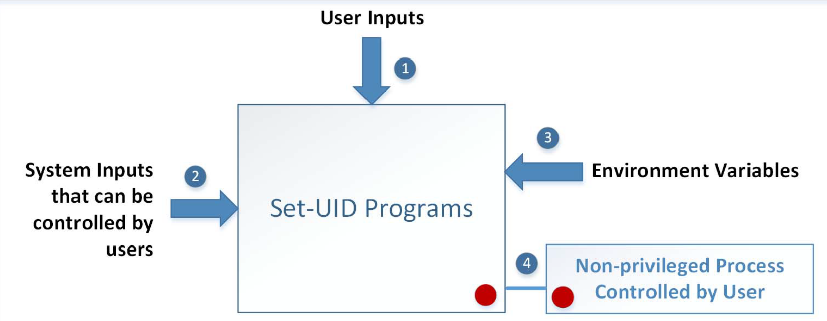
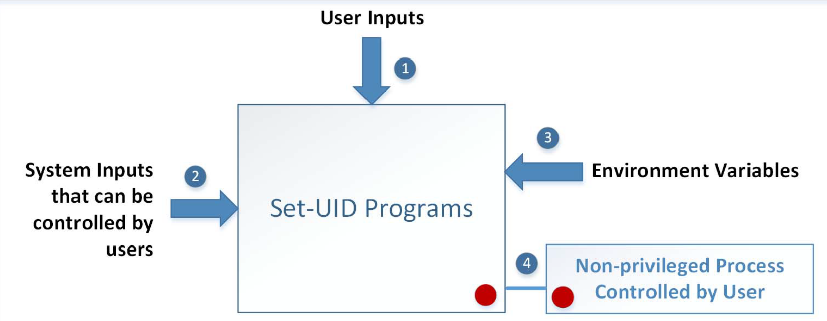
## Privileged Program
- A program that is executable by users
- carries elevated (administrative) power
- Example: `passwd`
- In Linux, passwords are stored in `/etc/shadow`
- Users need to be provided indirect access to modify
their passwords.
- Daemon (background processes) launched by privileged user ID (`root`).
- Utilize `Set-UID` mechanism of Linux to mark a program is privileged.
- Meaning that the program is owned by root but executable by users.
- Grant privilege to the task (process), not the user (using effective user ID)
<figure
>
<picture>
<!-- Auto scaling with imagemagick -->
<!--
See https://www.debugbear.com/blog/responsive-images#w-descriptors-and-the-sizes-attribute and
https://developer.mozilla.org/en-US/docs/Learn/HTML/Multimedia_and_embedding/Responsive_images for info on defining 'sizes' for responsive images
-->
<source
class="responsive-img-srcset"
srcset="/assets/img/courses/csc302/os-security/01-480.webp 480w,/assets/img/courses/csc302/os-security/01-800.webp 800w,/assets/img/courses/csc302/os-security/01-1400.webp 1400w,"
type="image/webp"
sizes="95vw"
>
<img
src="/assets/img/courses/csc302/os-security/01.png"
width="50%"
height="auto"
alt="Two-tiered access control"
data-zoomable
loading="lazy"
onerror="this.onerror=null; $('.responsive-img-srcset').remove();"
>
</picture>
</figure>
~~~bash
id
which id
cp /usr/bin/id ./myid
ls -l ./myid
sudo chown root myid
./myid
sudo chmod 4755 myid
./myid
~~~
- We want to use `cat` to view `/etc/shadow` as a normal user.
~~~bash
cat /etc/shadow
~~~
- Standard execution is not possible. We need more privileges
~~~bash
cp $(which cat) ./mycat
sudo chown root mycat
sudo chmod 4755 mycat
./mycat /etc/shadow
~~~
- `cp $(which cat) ./mycat`: Create a copy of `cat` called `mycat`
- `sudo chown root mycat`: Set the owner of `mycat` to be `root`
- `sudo chmod 4755 mycat`: This is a setuid mechanism - run `mycat` as its owner,
not as the user.
|